The Evolution of Data Security Threats and How to Address Them
25 March 2026
In today's digital age, data security threats have evolved from simple cyber nuisances to sophisticated attacks capable of crippling businesses and exposing sensitive personal information. With hackers getting smarter and technology advancing at a rapid pace, staying ahead of cyber threats is an ongoing battle. But what exactly has changed, and how can we protect ourselves?
In this article, we’ll dive deep into the evolution of data security threats, the latest tactics used by cybercriminals, and the best ways to stay secure in an increasingly connected world.
The Early Days of Cyber Threats
The internet wasn’t always the battleground it is today. Back in the early days of computing, most threats were relatively harmless. Think of prank viruses that displayed funny messages rather than stealing your credit card information.The First Cyber Attacks
Early cyber threats were more about curiosity and mischief than financial gain. The first known computer virus, the Creeper virus, appeared in the 1970s. It didn’t steal data or cause damage—it simply displayed the message: _"I'm the Creeper, catch me if you can!"_. Harmless, right?But as technology advanced, so did the motives behind cyber threats. Hackers transitioned from playful experiments to malicious intent, leading to a new era of cybercrime.
The Rise of Malware and Phishing Attacks
The 90s and early 2000s saw a massive boom in internet adoption, and with it came a rise in cyber threats. Suddenly, viruses weren’t just for fun anymore—they became tools for financial fraud, corporate espionage, and identity theft.Malware Becomes Mainstream
Malware, short for "malicious software," became a primary weapon for hackers. Familiar names like Trojans, worms, and spyware started showing up on millions of computers worldwide.- Trojans disguised themselves as legitimate software.
- Worms spread rapidly between devices without user intervention.
- Spyware secretly collected users' personal information.
The goal? Data theft, financial fraud, and control over computers without the user's knowledge.
Phishing Schemes Take Over
By the early 2000s, phishing scams became one of the most successful cyber attack methods. Hackers would disguise themselves as trusted entities—like banks or social media platforms—to trick users into giving away passwords and financial details.Remember those sketchy emails from "your bank" asking you to log in urgently? Many people fell victim to those tactics, leading to millions in stolen funds and personal data leaks.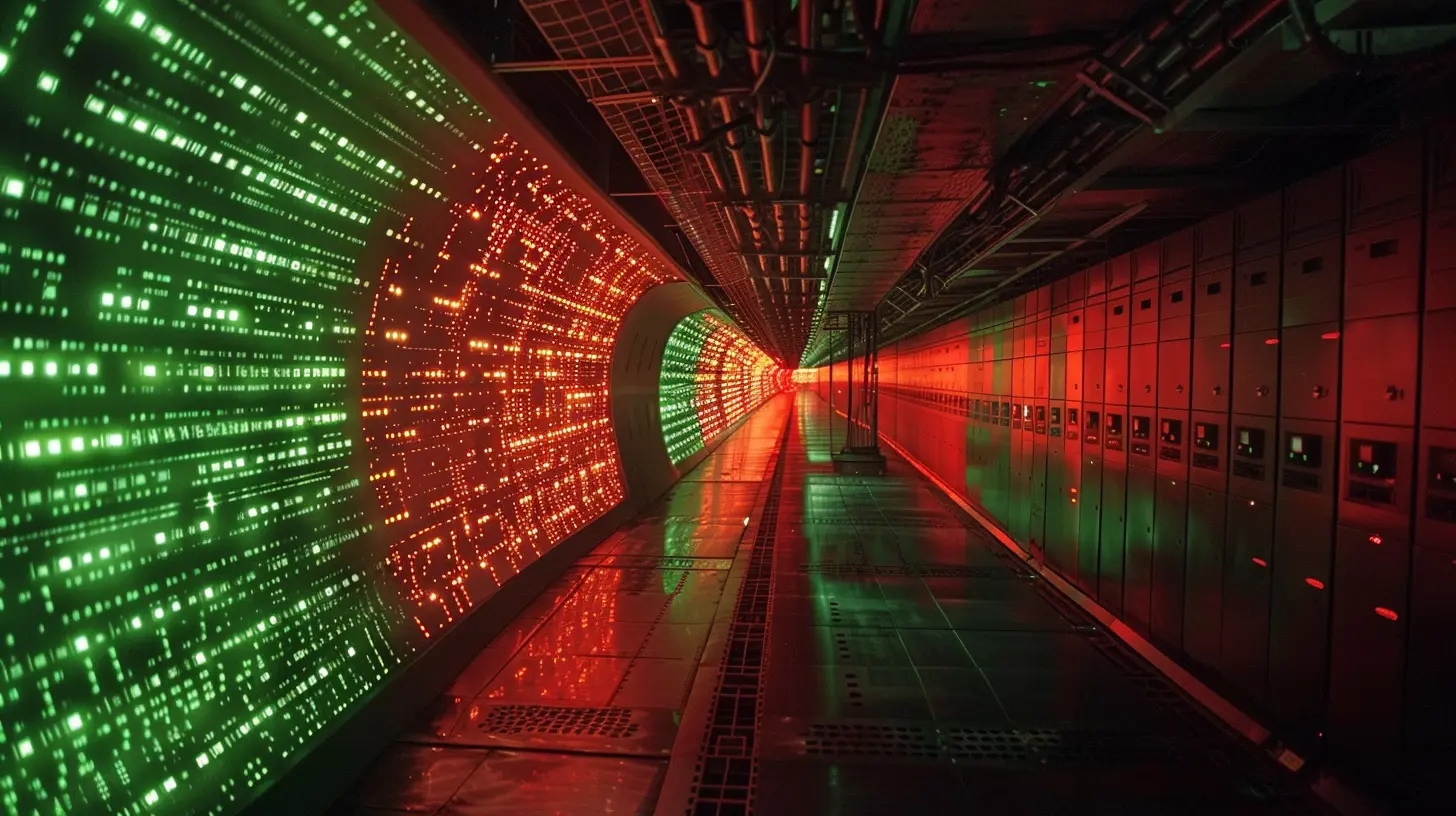
The Age of Ransomware and Sophisticated Cyber Attacks
Fast forward to the 2010s, and cybercriminals had leveled up. Simple phishing emails evolved into highly-targeted attacks, and new threats started emerging, causing massive disruptions worldwide.Ransomware Spreads Like Wildfire
One of the most devastating cyber threats of the past decade has been ransomware attacks. WannaCry, NotPetya, and other high-profile ransomware strains have caused billions of dollars in damages globally.How does ransomware work? It encrypts files on infected devices and demands a ransom for their release. If victims don’t pay up, they risk losing everything.
Advanced Persistent Threats (APTs)
Cybercriminals were no longer just individual hackers in basements. Organized cybercrime groups and nation-state hackers started deploying Advanced Persistent Threats (APTs)—long-term, stealthy cyberattacks aimed at governments, corporations, and critical infrastructure.APTs don’t make noise like common viruses. Instead, they infiltrate networks quietly, stealing valuable intellectual property, trade secrets, or classified government data for months or even years without detection.
The Modern Cyber Threat Landscape
As we step into the 2020s, cyber threats have become more complex than ever. Attackers are using AI-powered hacking techniques, deepfake technology, and even exploiting IoT devices to gain access to sensitive data.Cloud Security Breaches
With companies moving to the cloud, hackers follow. Poor cloud security configurations, mismanaged access controls, and human errors have led to some of the biggest data breaches in history.Popular cloud-based services like Google Drive and AWS are attractive targets. If one account is compromised, entire business operations can be at risk.
AI-Powered Cyber Attacks
Artificial Intelligence has given hackers a dangerous new tool—automation. AI-driven cyber attacks can analyze security defenses, find vulnerabilities, and launch attacks at a scale never seen before.Cybercriminals can now:
- Generate deepfake phishing emails that look eerily real.
- Automate exploits to breach systems faster.
- Launch AI-powered brute force attacks to crack passwords in seconds.
IoT Vulnerabilities
With the rise of smart devices—like security cameras, smart TVs, and even connected refrigerators—cybercriminals have more entry points than ever.Many IoT devices lack strong security measures, making them easy targets for hackers to exploit. Unsecured smart home devices can become part of massive botnets that contribute to DDoS attacks, crippling websites and online services.
How to Address These Evolving Threats
Now that we’ve covered how cyber threats have evolved, let’s talk solutions. How can you protect your data in this age of ever-growing cyber risks?1. Strengthen Password Security
Weak passwords are still one of the biggest security risks out there. Here’s what you can do to keep your accounts safe:- Use long, complex passwords with a mix of letters, numbers, and symbols.
- Enable two-factor authentication (2FA) whenever possible.
- Consider using a password manager to store and generate secure passwords.
2. Keep Software and Systems Updated
Outdated software is an open invitation for cybercriminals. Always ensure:- Your operating system, apps, and antivirus software are updated.
- Security patches are installed as soon as they’re released.
- Legacy systems that no longer receive updates are replaced.
3. Be Wary of Phishing Attacks
Phishing attacks are still one of the most effective cyber threats today. To avoid falling victim:- Never click on suspicious links in emails or messages.
- Double-check email addresses before responding to sensitive requests.
- Verify calls and emails from banks or government institutions before providing any information.
4. Secure Cloud and IoT Devices
If you’re using cloud storage or smart devices, take these precautions:- Enable multi-factor authentication (MFA) for all cloud accounts.
- Regularly audit permissions for cloud storage and restrict unnecessary access.
- Change the default passwords on smart devices to strong, unique ones.
- Keep IoT devices updated with the latest firmware.
5. Implement Network Security Best Practices
For businesses and individuals alike, securing networks is crucial:- Use firewalls and intrusion detection systems (IDS) to monitor traffic.
- Run regular security audits to detect vulnerabilities.
- Encrypt sensitive data before storing or transmitting it.
Final Thoughts
Data security threats have come a long way since the playful viruses of the 70s. Today, cybercriminals are smarter, faster, and more relentless than ever. But that doesn't mean we have to live in fear.By adopting good cybersecurity habits, staying informed, and using the latest security tools, we can stay one step ahead of hackers. Remember, cybersecurity isn’t a one-time fix—it’s a continuous effort.
So, are you ready to take your data security seriously? Because in this ever-evolving digital world, being prepared is the best defense.
all images in this post were generated using AI tools
Category:
Data SecurityAuthor:
Reese McQuillan
Discussion
rate this article
2 comments
Flint Mercado
Insightful overview of evolving threats.
March 28, 2026 at 1:31 PM
Reese McQuillan
Thank you! I'm glad you found it insightful.
Nora Mahoney
This article provides a comprehensive overview of the shifting landscape of data security threats. The insights on evolving tactics and proactive measures are particularly valuable for organizations striving to safeguard sensitive information. Thank you for shedding light on such an important topic in our increasingly digital world!
March 28, 2026 at 5:19 AM
Reese McQuillan
Thank you for your thoughtful feedback! I'm glad you found the insights valuable for enhancing data security in today's digital landscape.


