The Growing Importance of Hardware Security Modules in Data Protection
10 March 2026
In today’s digital world, data security is more crucial than ever. Every day, businesses and individuals generate massive amounts of sensitive data that need to be protected from cybercriminals. One of the most effective tools for securing this data is a Hardware Security Module (HSM).
But what exactly is an HSM? Why is it becoming so important in data protection? And how can it help safeguard your business? Let’s break it all down in a simple and engaging way. 
What is a Hardware Security Module (HSM)?
At its core, a Hardware Security Module (HSM) is a physical device designed specifically to manage cryptographic keys and protect sensitive information. Think of it like a high-security vault—but instead of storing cash or gold, it holds the digital keys that keep your data safe.HSMs handle encryption, decryption, authentication, and digital signing processes. They’re built with tamper-resistant hardware, making it nearly impossible for hackers to access the stored keys, even if they get their hands on the device itself. 
Why is Data Protection More Important Than Ever?
Let’s be real—cyber threats are evolving at an alarming rate. Businesses store everything online: from customer details and payment info to trade secrets. Hackers are constantly looking for ways to exploit weak security systems.Here’s why data protection should be a top priority:
- Increase in Cybercrime – Data breaches and ransomware attacks are becoming more frequent. A single cyberattack can cost millions and ruin a company’s reputation.
- Stricter Regulations – Governments worldwide are enforcing stricter rules on data security, with hefty fines for non-compliance. Laws like GDPR, CCPA, and PCI DSS require robust data protection measures.
- Rising Cloud Adoption – As more businesses shift to cloud-based services, the need for advanced security measures (like HSMs) grows exponentially.
Now that we understand the urgency, let’s dive into how HSMs play a critical role in enhancing data security. 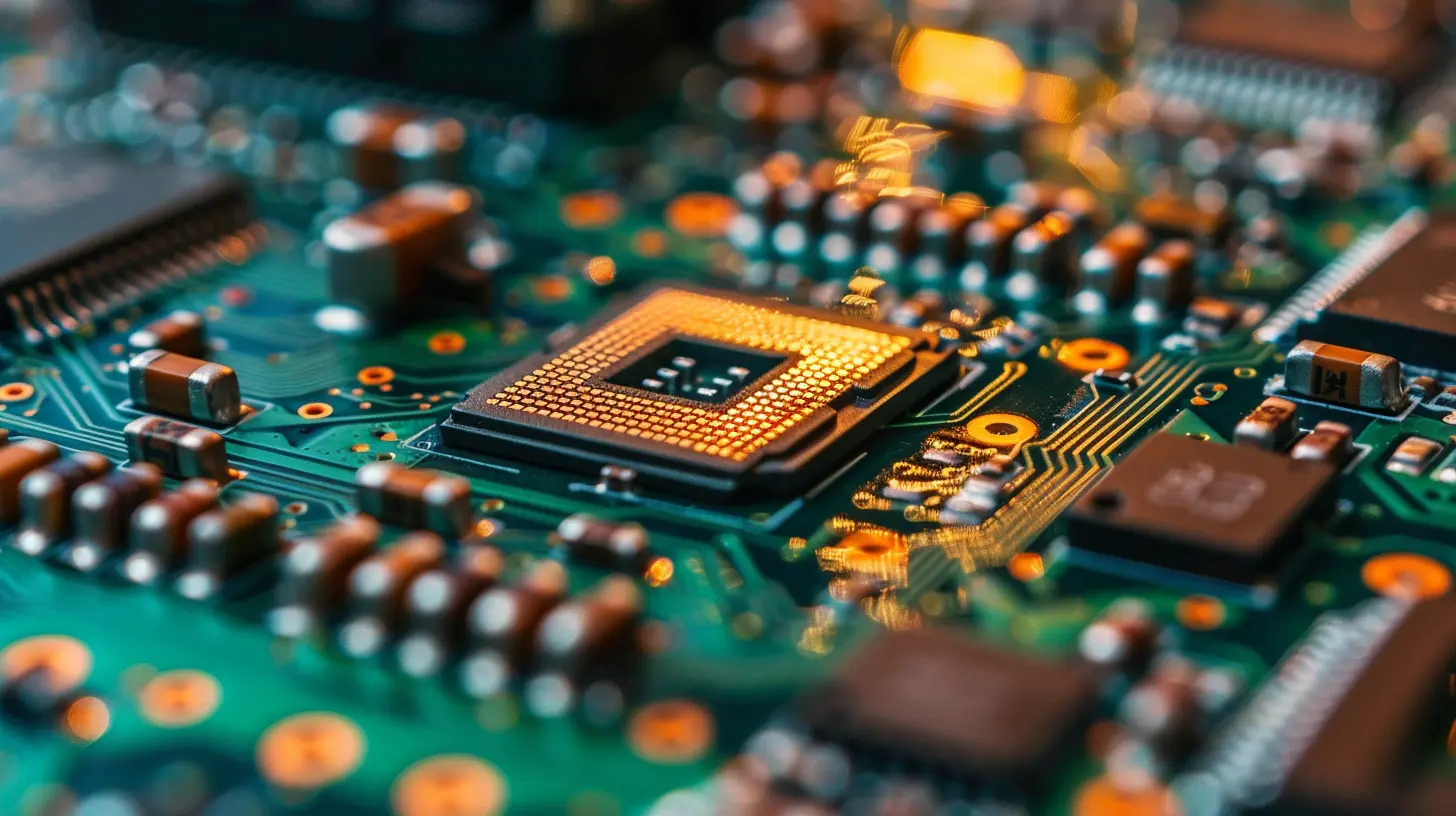
How Hardware Security Modules Protect Sensitive Data
HSMs are like an unbreakable lock for your most critical data. Here’s how they help keep information safe:1. Strong Cryptographic Key Management
Encryption is only as strong as the keys that protect it. HSMs generate, store, and manage cryptographic keys in a secure environment. By keeping encryption keys safe from unauthorized access, they ensure that even if attackers get their hands on encrypted data, they won’t be able to decrypt it.2. Secure Authentication
Many organizations use multi-factor authentication (MFA) to add an extra layer of security. HSMs store authentication credentials securely, preventing unauthorized access to critical systems.3. Tamper-Resistant Protection
One of the most impressive features of an HSM is its tamper resistance. If someone attempts to physically interfere with the device, it automatically wipes all stored keys, making data theft nearly impossible.4. Compliance with Security Standards
Many industries have strict security compliance requirements. HSMs help organizations meet regulatory standards such as:- Payment Card Industry Data Security Standard (PCI DSS)
- General Data Protection Regulation (GDPR)
- Federal Information Processing Standards (FIPS 140-2 & 140-3)
If a company fails to comply with these regulations, they could face severe financial penalties. HSMs provide a strong foundation for meeting these security mandates.
5. Protection Against Insider Threats
While external hackers are a big concern, insider threats can be just as dangerous. HSMs limit access to cryptographic keys to authorized personnel, reducing the risk of internal fraud or accidental exposure.
The Growing Demand for HSMs in Different Industries
HSMs are no longer just for government agencies and large financial institutions. Companies across various industries are realizing their value. Here are a few sectors where HSM adoption is rapidly increasing:1. Banking and Finance
Banks deal with massive amounts of sensitive financial data daily. HSMs help protect transactions, secure customer information, and ensure compliance with strict regulations like PCI DSS.2. Healthcare
With hospitals and healthcare providers adopting digital records, patient confidentiality is critical. HSMs help protect electronic health records (EHRs), ensuring compliance with regulations like HIPAA.3. E-Commerce and Online Payments
Online businesses handle thousands of transactions every day. HSMs safeguard payment processing systems, preventing fraud and securing customer data.4. Cloud Service Providers
As businesses move to the cloud, the risk of cyber threats increases. Leading cloud providers integrate HSMs to offer encrypted storage and secure data access.5. Government and Defense
Governments use HSMs to protect classified information, secure communication, and prevent cyber espionage.Cloud-Based HSMs: A Game Changer
Traditionally, HSMs were physical devices installed on-premises. But today, businesses are adopting Cloud HSMs—a more flexible and scalable option.Why go for a Cloud HSM?
- Cost-Effective – No need for expensive hardware; pay as you go.
- Scalability – Adjust security measures as your business grows.
- Remote Management – Secure data encryption for remote teams and global businesses.
Leading cloud providers like AWS CloudHSM, Google Cloud HSM, and Microsoft Azure HSM offer enterprise-level security without the complexity of managing physical hardware.
Challenges of Implementing HSMs
While HSMs are incredibly effective, they do come with a few challenges:- High Initial Costs – On-premise HSMs require a significant upfront investment.
- Technical Complexity – Managing cryptographic keys and integrating HSMs into existing systems can be complex.
- Training & Expertise – Organizations need skilled professionals to handle HSM operations effectively.
Fortunately, cloud-based solutions are making HSM adoption more accessible and cost-effective.
Should Your Business Invest in an HSM?
If your business handles sensitive data—customer records, financial transactions, confidential contracts—you need solid security measures. An HSM might just be your best defense against cyber threats.Ask yourself:
- Do you need strong encryption for your data?
- Are you handling sensitive customer information?
- Do you need to comply with regulations like PCI DSS or GDPR?
If you answered yes to any of these, investing in an HSM could be a game-changer for your data security strategy.
Final Thoughts
In the ever-evolving landscape of cybersecurity, Hardware Security Modules (HSMs) have proven to be a crucial tool for protecting sensitive data. Whether you're running a bank, an e-commerce store, or a healthcare institution, securing your cryptographic assets should be a top priority.With the rise of cloud computing, Cloud HSMs are making high-level security more accessible than ever, helping businesses strengthen their defenses without breaking the bank.
Cyber threats aren’t slowing down, but with the right security approach—like integrating an HSM—you can stay one step ahead of hackers and keep your most valuable data safe and sound.
all images in this post were generated using AI tools
Category:
Computer HardwareAuthor:
Reese McQuillan
Discussion
rate this article
2 comments
Jinx McCool
This article effectively highlights the crucial role Hardware Security Modules play in enhancing overall data protection strategies.
March 19, 2026 at 3:23 AM
Solara McQuillen
Hardware Security Modules are essential for robust data protection, providing a secure environment for cryptographic keys and safeguarding sensitive information against cyber threats.
March 10, 2026 at 12:18 PM
Reese McQuillan
Thank you for your insightful comment! Indeed, Hardware Security Modules play a vital role in enhancing data protection by securely managing cryptographic keys and defending against cyber threats.


